Without a mobile device security policy, your IT staff will tell you that it’s a free for all. Many organizations allow their employees to connect to corporate networks (especially for email) with their personally owned laptops and cell phones. This creates huge issues in terms of managing and securing the corporate data that ultimately can find its way onto these devices.
A good policy serves to educate the workforce and set boundaries for what is acceptable in terms of equipment and behavior.
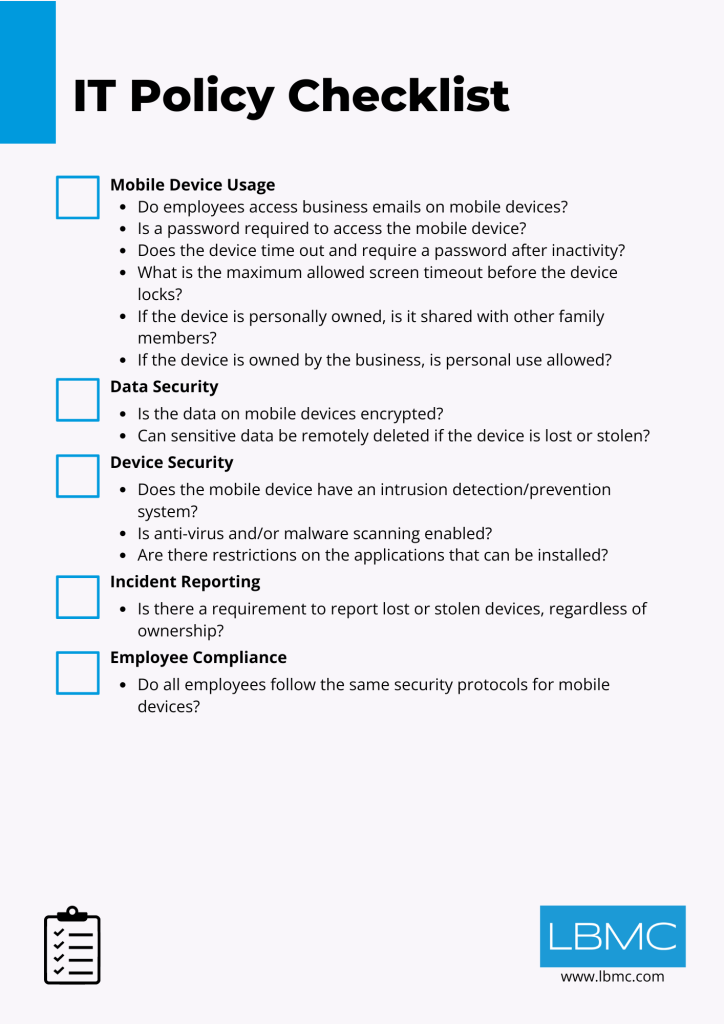
One of the first questions to be answered is, “Are we going to allow our employees to access corporate systems with their personal laptops and/or smartphones?” Every business is different as are the risks. However, there are some significant benefits to allowing only corporately issued devices to connect. They include:
- Device tracking and monitoring including retrieval of the device upon termination.
- The ability to have standard configurations that include security controls such as encryption, passwords, etc. (you can sometimes enforce these with non-corporate devices, but it ’s easier if they are provisioned by the IT group).
- Fewer compatibility issues.
- Reduced support burden for the help desk.
Regardless of your decision related to the use of personal equipment, there are some universal considerations. If your organization houses sensitive data or data that is “protected” such as patient records, personal financial information, or information that could be used by identity thieves, you will want to take a more proactive approach to secure mobile devices.
For laptop computers, this means at a minimum the use of unique user IDs and strong passwords. With the ubiquity of the technology, full disk encryption should also be strongly considered. While not necessarily a regulatory requirement, encryption provides a “safe harbor” from having to report a breach under some data breach laws, including HIPAA/HITECH. For smartphones, consider mandating the following technical security controls in your policies:
- Encryption of data stored on the device
- A requirement for a password for access to corporate systems (e.g. email, VPN, etc)
- Screen timeout with password required to re-access the device
- Remote wipe feature enabled after a specified number of failed login attempts
- Remote wipe feature if the phone is lost/stolen
From an administrative standpoint, there are also things that are important to include or reference in your mobile device policy. Some of these include:
- Appropriate use
- Download of unauthorized software
- Procedures to report a lost/stolen/found device
- Use in public Bluetooth and wireless environments
It is worth saying that it’s not if someone will lose their laptop or phone, but when. Since we know at some point we’ll be on the losing end of the old playground adage, with a little work we can cut out the weeping.