Key Takeaways
- Risk assessments are basic for compliance in areas such industry and healthcare, so guaranteeing that legal obligations and strategic protections are fulfilled.
- Strategic risk management of cybersecurity risks is made possible by proactive identification, assessment, and mitigating action.
- Risk assessments help to match cybersecurity initiatives with corporate objectives, thereby improving general security posture and optimizing resource use.
Risk Assessments
Performing risk assessments and overseeing risk management programs are essential skills for anyone in cybersecurity. Many cybersecurity frameworks and regulations require a risk assessment, including, but not limited to:
Cybersecurity Frameworks
- Collective Controls Catalog (v2021, v2022, v2023)
- NIST Cybersecurity Framework (v1.0, v1.1, v2.0)
- ISO 27002:2005, 27002:2013, 27002:2022
- NIST Special Publication 800-171
- NIST Privacy Framework (v1.0)
- Factor Analysis of Information Risk (FAIR)
- Department of Defense (DoD) Risk Management Framework (RMF)
- Cybersecurity Maturity Model Certification (CMMC) – Level 2
- Cloud Security Alliance Cloud Control Matrix (CSA-CCM v3.0.1 and v4.0)
- Farm Credit Administration (FCA) Examination Manual (v2022)
- Payment Card International (PCI) Data Security Standard (DSS) (v3.2.1 and v4.0)
- US Securities and Exchange Commission (SEC) 2023 Cybersecurity Disclosure Rules (v2023)
Regulations
- Health Insurance Portability and Accountability Act (HIPAA)
- General Data Protection Regulation (GDPR)
- California Consumer Privacy Act (CCPA)
- Gramm–Leach–Bliley Act (GLBA)
- Personal Information Protection and Electronic Documents Act (PIPEDA)
- Protection of Personal Information Act (POPI)
- Internal Revenue Service (IRS) Publication 1075
- New York Cyber Security Regulation (23 NYCRR 500)
- General Personal Data Protection Act (LGPD)
- New York Department of Financial Services (NYDFS)
- FTC Safeguards Rule
With technology and cybersecurity threats evolving quickly, all businesses must know how to evaluate and handle risks effectively. Let’s explore the key parts of risk assessments and management and provides practical tips to improve security measures and make better choices.
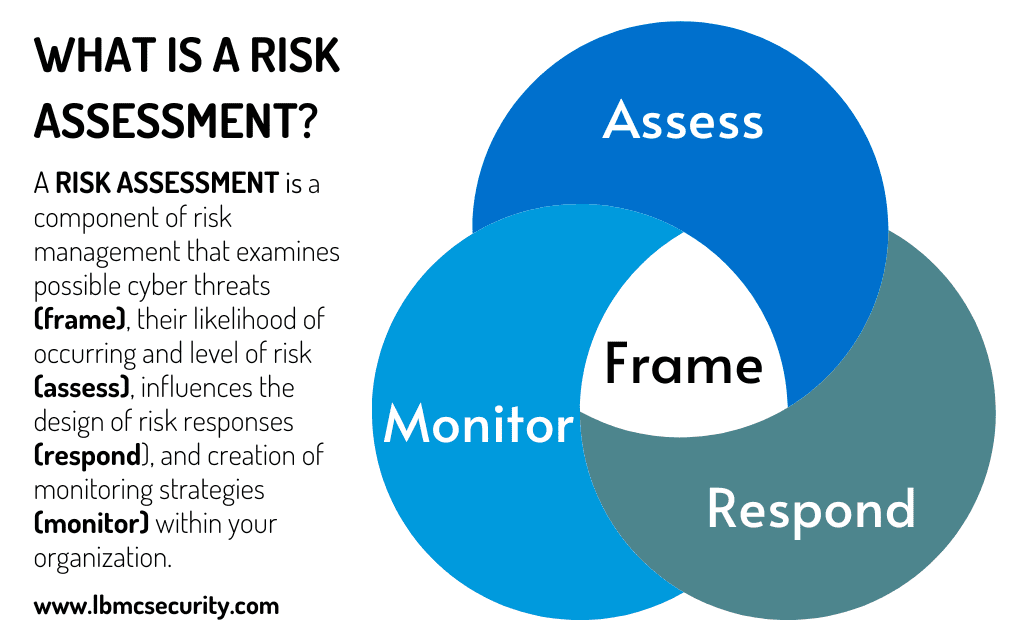
What is a Risk Assessment?
A risk assessment is a component of risk management that examines possible cyber threats (frame), their likelihood of occurring and level of risk (assess), influences the design of risk responses (respond), and creation of monitoring strategies (monitor) within your organization.
These assessments are absolutely essential initial step in deciding where to deploy money and personnel to reduce vulnerabilities and lessen cybersecurity risk. Identifying organizational hazards helps to set the stage for a comprehensive risk control program. This proactive risk assessment strategy makes targeted risk management training possible, therefore enabling a move from reactive to proactive approaches.
Why Do Risk Assessments Matter?
Institutions in all kinds as well as cybersecurity experts depend on risk assessments. They enable informed decision-making, therefore improving the distribution of resources and a more effective way of managing threats. When a risk assessment is performed, it helps identify potential risks within an organization by laying down a foundation for a risk management strategy and highlighting areas where training and improvement are needed. Being proactive regarding possible risks and vulnerabilities is imperative for organizations to stay ahead of threats and mitigate security gaps.
Especially as the technology business environment changes, regular risk assessments guarantees that companies remain on top of relevant risks and compliance rules.
Risk assessments are top priority for cybersecurity experts for several important reasons.
- Legal and Regulatory Compliance: Many disciplines demand regular risk assessments; they are not only advise. For example, evaluating risks is legally required in the American healthcare system. Legal, retail, and manufacturing are just a few of the sectors this need spans; each has policies or responsibilities for regular risk assessment.
- Best Practices: Protecting assets and data depends on first understanding and control of cybersecurity risks. It is a fundamental practice in cybersecurity to measure and understand risks and manage them effectively. This understanding helps defend against potential threats more efficiently and promptly.
- Alignment with Business Goals: Conducting risk assessments ensures that security measures align with the business’s broader objectives. This alignment aids in utilizing resources more effectively and supports the organization’s overall goals. Business leaders often better understand risk management and specific technical vulnerabilities, making risk assessments vital in bridging this knowledge gap.
Developing a strong risk management plan starts with knowing why risk assessments are so important and the advantages they bring. This approach not only protects against possible risks but also fits the general goals of your company, thereby guaranteeing development and stability in an always changing digital world.
Improving Security Using a Formal Risk Analysis Approach
For companies, moving from an informal to a formal risk assessment procedure is absolutely essential. It is not just about following procedures; it significantly improves risk management. For the reasons outlined below, adopting a formal risk assessment process is crucial for security professionals.
Benefits of a Formalized Risk Assessment Process
Security departments that are knowledgeable and informed regarding vulnerability remediation but do not have defined risk assessment processes may find the journey from recognizing gaps to implementing a structured risk assessment process overwhelming at first glance. Organizations often realize they have been spotting risks and identifying vulnerabilities throughout the environment, even in areas lacking defined processes. This emphasizes an important point: security personnel naturally identify risks; however, these risks can go undocumented and unaddressed without formalizing the risk assessment process. Formalized risk assessment procedures help to detect weaknesses and their fixing initiatives even more successfully.
Sharing Risks with Leaders
Risk management in cybersecurity mostly aims to give vital information for executive decision-making rather than to stop corporate projects. With structured risk assessments, insights into security vulnerabilities become extremely valuable for informing key decision-makers and business leaders. This communication ensures that decisions are made with an awareness of risks, a deep understanding of what those risks mean, and a recognition of the inherent dangers associated with those risks.
Six Essential Steps for Establishing an Effective Cybersecurity Risk Assessment Process
A formal risk assessment involves recording everything associated with the risks of a workplace or environment. A great resource for learning how risk assessments are performed is The National Institute of Standards and Technology’s Guide for Conducting Risk Assessments. Fundamentally, the following describes the procedures to establish a formal risk assessment mechanism:
Step 1: Identify Risks
Finding risks includes realizing possible hazards connected to corporate projects, fresh IT innovations, or major organizational adjustments. This covers assigning pertinent threat occurrences and classifying possible sources of risks including antagonistic, accidental, structural, and environmental ones.
Organizations should list possible threat sources and ascertain particular threat occurrences, such phishing campaigns or natural disasters, so properly identifying hazards. This thorough procedure guarantees that every conceivable risk is identified for more investigation.
Step 2: Identify Vulnerabilities
Finding vulnerabilities allows one to grasp how risks could take advantage of organizational flaws. This stage evaluates current security posture and factors that can let the company be vulnerable to failures or attacks.
Organizations should do technical penetration testing and a current state analysis against security models such as NIST CSF. Sort and fully grasp vulnerabilities using NIST 800-30 Appendix F.
Step 3: Evaluate the Risks
Analyzing found risks helps one to comprehend their possible influence and rank them according to probability and importance. This stage helps companies to concentrate on the most important hazards and distribute their resources properly.
Using NIST 800-30 guidelines, one can estimate the probability of each threat event leading to a loss and analyze the possible impact. This dual study offers a thorough image of the risk scene of the company.
Step 4: Calculate Risk
Calculating risk helps to prioritize found hazards by quantifying their possible impact and probability of occurrence. This stage aggregates assessments to create a risk value, hence guiding efforts at strategic risk management.
As stated in NIST 800-30 Appendix I, integrate likelihood and impact values using a 9-block matrix. This methodical technique prioritizes risks from high to low priority, therefore guaranteeing that the most critical are handled first.
Step 5: Mitigate the Risks
Developing and applying plans to control found hazards helps the company to be free from possible risks. This step ensures the organization can maintain operations and security posture.
Develop comprehensive risk mitigation plans addressing high-priority risks, including specific actions like implementing security controls and training staff. Regularly review and update plans to adapt to changing threats.
Step 6: Communicate the Risks
Communicating risks ensures all stakeholders are informed about the organization’s risk landscape and mitigation strategies, fostering a risk-aware culture. Good communication helps attempts at risk management on all levels.
Write thorough risk assessment reports and distribute them, via frequent briefings, to stakeholders and leaders. Effective risk management techniques depend on clear, succinct communication guaranteeing understanding and agreement.
The objective is not to get every recommendation approved but rather to guarantee that every decision is based on a thorough awareness of the hazards and weaknesses entailed.
Beyond Compliance
Although satisfying legal requirements is important, the real goal of a risk analysis is to support management in deciding which security policies the company needs. This viewpoint actively securing organizational assets and information replaces checking boxes for compliance checklists.
For every security team, implementing a formal risk assessment system represents a major improvement. Risk assessments help to spot, examine, and explain risks so enhancing the decision-making process all around the company. This is about enhancing security’s strategic role while negotiating a challenging risk environment, not about increasing documentation. An assessment invites security professionals to respond to risks, actively manage and reduce risks, and guide the organization through careful planning and foresight.
Risk Assessment vs. Risk Management
For cybersecurity employees and personnel, figuring out the distinction between a risk assessment and risk management can be tricky. For clarity, these can both be defined as:
- Risk Assessment: A risk assessment is used to figure out how probable an incident is to happen and how severe it could be if it does. One key word in that definition is “probable” – the possible frequency and magnitude. Dealing with risk calls for a fundamental understanding of probability.
- Risk Management: Risk management is the addressing and control of risks from identification to remedial action. This procedure consists on spotting hazards, analyzing their influence, choosing the best course of action to fix the problem, and determining the main cause. Employees should use a set strategy or framework that directs the whole process if they are to properly control risks.
Risk management goes beyond risk assessments, which are essentially about spotting possible issues and their effects to actively handle and manage those risks using a whole strategy.
Risk Management: Good Remedial Strategies
A key component of risk management, risk remedial action is the process of addressing risks—from inside or outside of an entity. Risk remedial action refers to several methods one could lower, avoid, accept, or shift hazards off to another person. A few ways in which risks can be addressed include:
- Avoidance: The avoidance method involves staying away from risky activities. By not getting involved in certain things, organizations can dodge inherent risks.
- Acceptance: Organizations must recognize that certain risks exist in doing business. Companies cannot stop these risks but must prepare to deal with what happens when one of these risks presents itself.
- Mitigation: This strategy involves implementing measures to lessen the impact of risks. These measures could include safety steps, procedures, or protections.
- Transfer: With this strategy, organizations let someone else take on the responsibility of identified risk. This is often done through insurance, agreements, or cybersecurity insurance.
Risk Assessment Best Practices
Waiting for a flawless way to identify and measure all risks means that many risks will be ignored too long. There are several essential practices that most organizations should consider, no matter what industry they are in or what rules they need to follow. A few of these are:
- Organizations should understand that any type of risk assessment is better than none. When prioritizing risks, concentrate on how likely a threat will occur and the potential damage it could cause the organization. To simplify, think of risk assessments as the likelihood of the danger happening multiplied by its potential impact, which equals the level of risk. Following an assessment of every threat, the management team and corporate executives should first focus on those judged as most important.
- One should constantly assess these hazards throughout time. Companies should refrain from moving between several measuring techniques since this could result in an erroneous perception of risks and render tracking of development impossible. A steady, defined, documented process and rating system for each assessment will ensure consistency when gathering the necessary information to guide each organization effectively. Ultimately, helping the management team and business leaders make informed decisions about security risks is the most vital role a risk assessment can play. Once a quantitative method for assessing risk is established, consistency ensures reliable comparisons over time, facilitating effective decision-making. Deviating from the chosen method can introduce inconsistencies and undermine the accuracy of risk evaluations. Maintaining the chosen quantitative approach fosters familiarity among stakeholders, streamlining communication and enhancing the organization’s risk management effectiveness.
- Companies should be aggressive about forthcoming changes in risk variables and legal obligations affecting their business. One great approach is to interact with national or local business associations. By means of these associations, security experts can acquire knowledge about forthcoming developments, therefore enabling their preparation in advance. Industry magazines are another great source since reporters typically cover approaching developments before they take place. Another good way is to go to conferences and events, which provides direct contact with people engaged in industry transitions and an opportunity to talk about these developments among colleagues in a laid-back environment.
Risk Assessments Should Add Value
Security risks are seldom the top concern for an organization. Security professionals sometimes forget that the executive team has other priorities and responsibilities. Other business factors may influence the significance of security vulnerabilities and how the suggestions are received internally. Security professionals should try to see the bigger picture as much as possible. Once the security risks are shared with the leadership team, they must trust that they have fulfilled their responsibilities. Providing high-quality information, rather than just technical jargon, to those who might not grasp it ensures that risk assessments continue to add substantial value to the organization.
LBMC’s Risk Assessment Process
LBMC’s process for assessing risk focuses on the main aspects of cybersecurity. The steps LBMC utilizes for performing a risk assessment are:
- First, LBMC talks to and interviews the critical staff responsible for managing IT security and privacy.
- Next, LBMC will review the security rules, procedures, IT systems, records, and training content to compare them to the rules and regulations for each applicable industry.
- LBMC then performs automated and hands-on testing to check the information security system and spot potential problems.
- After gathering all this information, LBMC compiles a report on the current landscape and determines how the organization complies with other essential security standards and regulations.
- Finally, LBMC will provide a summary report for executives. This report clarifies the company’s progress toward strengthening its defense against cybersecurity threats and meeting legal requirements.
The LBMC methodology combines aspects of:
- NIST SP 800-30 Rev 1, “Guide for Conducting Risk Assessments.”
- Industry threat identification resources.
- Guidance disseminated by regulatory authorities
- NIST CSF Informative References
- Real-world experience conducting assessments for organizations in various industries, sizes, and security postures. Software solutions are also available to streamline your risk assessment process with an intuitive, automated tool.







