Key Takeaways:
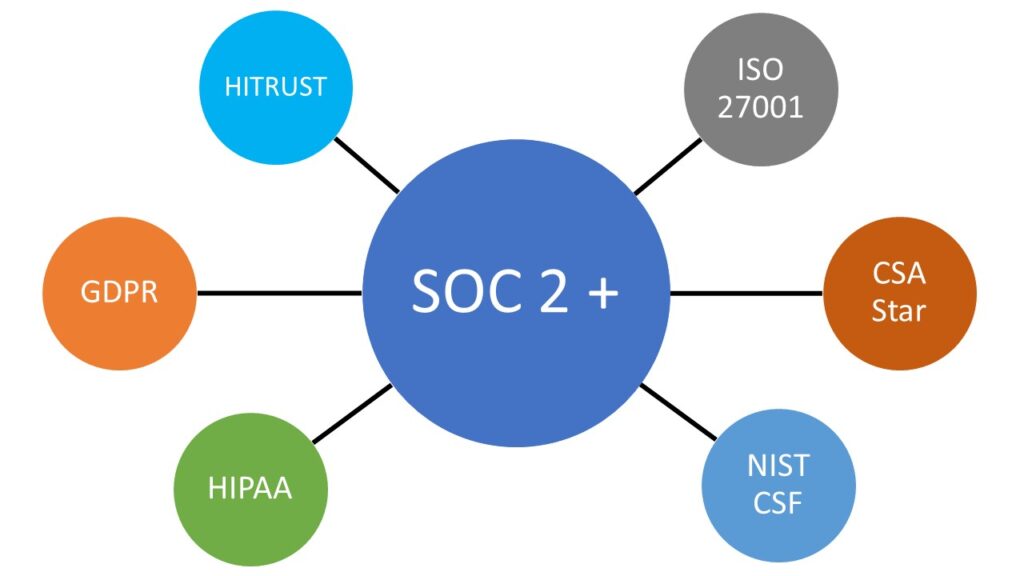
- SOC 2+ reports are a great way for organizations to demonstrate compliance with additional frameworks beyond the standard SOC 2, enhancing trust with clients and regulatory bodies.
- Incorporating SOC 2 with other frameworks, such as HIPAA or ISO 27001, can be accomplished through a SOC 2+ Examination, allowing organizations to show adherence to multiple compliance standards in a single report.
- SOC 2+ reports not only support regulatory compliance, but also serve as a strategic marketing tool, positioning service organizations advantageously against competitors in industries with rigorous data security requirements.
Why SOC 2+ Reports are Game-Changers for Service Organizations
As customer trust increasingly depends on robust data security, organizations providing services, such as the healthcare IT industry, are challenged by a variety of compliance requirements from their customers. Service organizations have regarded the System and Organization Controls (SOC) audit standards as a benchmark for demonstrating the security and privacy of their data handling practices.
As regulatory requirements broaden and the frequency of security questionnaires from customers increases, these organizations may struggle to find compliance reports that adequately address both regulatory demands and customer inquiries. One solution to consider is a SOC 2+ report.
Let’s discuss some of the benefits, requirements involved, and examples of SOC 2+ reports an organization could issue. We will also walk through an example scenario of an organization under pressure to prove its compliance with a regulation.
Why SOC 2 Compliance is Important
SOC 2 assessments are specifically designed for service organizations that handle sensitive customer data. These evaluations ensure that stringent security measures are in place to protect data, which is crucial not only for the safety of customer information but also for maintaining the integrity and reputation of the business. More companies are now making SOC 2 compliance a mandatory requirement for their vendors to strengthen their cybersecurity postures.
Advantages of SOC 2+ Reports
A SOC 2+ report extends the conventional SOC 2 framework to cover additional regulatory requirements or compliance frameworks. This type of comprehensive reporting is increasingly beneficial as it showcases an organization’s dedication to robust compliance standards across multiple frameworks, thus enhancing trust with clients and regulatory bodies.
Case Study: HIPAA Compliance Through SOC 2
You are working for a large healthcare technology company, and the Board of Directors has requested evidence the organization is compliant with the HIPAA Security Rule. Additionally, they have inquired about the need to obtain a “HIPAA Certification.” After clarifying that HIPAA is a regulation rather than a certification, you are tasked with identifying whether the organization is adhering to the requirements of the HIPAA Security Rule.
The organization has an established SOC 2 Type 2 program, which has been maintained for years and includes the Privacy Trust Services Criteria (TSC). However, you are uncertain whether this is sufficient or if efforts can be combined. As you reflect on this, an idea emerges: what if you could leverage the existing SOC 2 report to demonstrate compliance with the HIPAA Security Rule?
Including other frameworks within an established SOC 2 Report program is an excellent way for an organization to show its clients that it is adhering to, compliant with, or addressing parts or the whole of other frameworks.
In this scenario, an organization operating in the healthcare sector is likely to encounter HIPAA compliance requirements when handling patient data. Similarly, organizations working within specific government jurisdictions may have specific data privacy regulations or frameworks their clients are inquiring about.
A SOC 2+ other framework type of report may meet some or all these types of needs.
Another benefit of a SOC 2+ report is for marketing purposes. For example, if the competitors in your industry are using adherence to HIPAA as a selling point, addressing the HIPPA Security Rule through your SOC report may address some of those marketing needs.
After running your idea for a combined SOC and HIPAA effort by your colleagues, the marketing team is thrilled. They could use the report to effectively sell the organization’s security posture both to traditional clients who accept SOC and to potential new healthcare clients.
The compliance team is pleased because this effort could be used to demonstrate to regulators how the organization is compliant with HIPAA and potentially eliminate or reduce fines. Everyone seems happy, but now it is up to you to execute this.
Addressing Other Frameworks in a SOC Report
There are three primary ways to address other frameworks in your SOC report, each serving different purposes.
1. Reporting on Additional Frameworks in Non-Audited Sections
In Section V, “Other Information Provided by the Service Organization,” organizations have the opportunity to detail how they align with additional frameworks not covered in the auditor’s report. Although this section is not subject to the auditor’s direct evaluation, the auditor will still read it to make sure there are not any serious inconsistencies.
Implementation Example
For example, this could be done by including a mapping of the organization’s SOC controls to the other frameworks’ controls or parts of a regulation. It should be noted that this will not result in a SOC 2+ report.
2. Integrating Additional Frameworks in Audited Sections
Map the organization’s existing SOC 2 controls to associated controls or requirements from another framework. This would be shown in Section III, “Descriptions of Controls,” and in Section IV, “Tests of Controls.”
- Section III: The organization describes controls that meet both SOC and the other framework.
- Section IV: When testing controls, references are made to both SOC and the other framework’s control references, where appropriate.
Implementation Example
For example, you could map your SOC controls to an associated ISO control, and the auditor will test these controls like they would any SOC control. This will not result in a SOC 2+ report, as the auditor is not issuing an opinion on the organization’s design and operating effectiveness of controls to meet the other framework.
3. Electing for a SOC 2+ Examination
If the organization undergoing an audit wishes the report to have the auditor’s opinion cover another framework, process, or regulation, that otherwise would not be covered under the SOC 2 opinion, they may choose a SOC 2+ Examination.
Report Implications
In this type of report, the auditor would form an opinion on whether controls implemented by the organization meet SOC and the other criteria or framework. If any controls are left out of the framework, the auditor’s opinion would reflect this omission, unless the auditor determines the omission to not be relevant to the organization or system.
Implementation Example
To test the additional framework, the organization would need to develop controls and implement controls from the other frameworks to address both the SOC and the other framework being assessed. In turn, the auditor would need to develop tests for these additional controls.
Qualifications and Implications of SOC 2+ Reports with Other Frameworks
Understanding Exceptions and Qualifications
Any exception here may result in qualification unless the auditor determines the exception is not material to the requirements of the framework. If there is an exception on a framework-specific control and the organization is already certified by the group the framework is sourced from, it will not be material.
SOC 2+ Report Limitations and Advantages
An important note here is that by doing a SOC 2+ report, you are not achieving a certification with the governing body of the other framework. It can, however, show how the organization is meeting service commitments to be compliant with other frameworks.
Practical Steps for SOC 2+ HIPAA Compliance
You contact your auditor, who confirms that obtaining a SOC 2+ HIPAA report is feasible. However, you will need to map your organization’s existing controls to the applicable requirements of the HIPAA Security Rules. Additionally, you must define new controls to address any gaps, and all controls will need to be tested.
Initiating the SOC 2+ HIPAA Compliance Process
Further, Section III will have to be expanded and the scope must be defined to cover storage, transmission, etc. of PHI that had not been in scope for SOC efforts. Despite all the challenges and work involved, you see it is possible to combine the efforts and you set out on the SOC 2+ HIPAA journey.
Integrating SOC 2 with Other Frameworks
While theoretically almost any framework could be turned into a SOC 2+ given sufficient controls to cover any areas the SOC TSCs do not cover, some frameworks naturally work better and already have mappings available.
SOC 2+ HITRUST
Through collaboration by HITRUST and the AICPA, a mapping between the two frameworks exists which maps the HITRUST CSF controls to SOC criteria for Security, Availability, Integrity and Confidentiality.
The scope for a HITRUST Assessment will be any system that stores or processes covered information. So, if your existing SOC scope does not cover all systems that process covered information, it may bring additional systems into scope.
For example, if an analytic tool is used to process covered information that may not be providing services to customers but holds patient data, it may bring that system into scope.
As a HITRUST Authorized External Assessor Organization for over 10 years, our team can guide you through the characteristics associated with SOC 2 and HITRUST assessments and the differences between them.
SOC 2+ ISO 27001
There are many ISO controls that map to one or more SOC criteria. However, not all do so new controls would need to be added to ensure the organization meets all ISO controls required for each objective. The controls that do map touch all 5 TSCs.
The scope of ISO 27001 covers the organization’s Information Security Management System, which is determined by conducting a risk assessment of the information the organization is protecting. As such, a SOC 2+ ISO report would need to cover both the intended SOC scope and the ISO scope of the organization’s Information Security Management System.
SOC 2+ CSA Star
About two-thirds of the Cloud Controls map either fully, or partially, over to the SOC TSCs. As such, the organization would have to review controls and potentially add additional controls to cover the full and partial gaps.
For example, this could mean updating controls to define a frequency that is in line with the CSA Star or adding a new control to cover a specific risk with working in a cloud environment addressed in the CSA. The mapped controls cover all TSCs.
The scope of a CSA Star Audit would cover all cloud resources an organization is using to provide its cloud services.
SOC 2+ NIST CSF
Almost all of the NIST CSF Subcategories can be mapped to the SOC TSCs, so any subcategories which do not directly map over would require additional controls to be identified. The controls that do map over, map to Security, Availability, and Confidentiality criteria.
The scope of NIST CSF covers the entire organization, so if your SOC scope is limited, your NIST CSF scope would also be limited. These items would be identified within the report.
Additionally, the NIST CSF aligns with certain regulatory requirements, such as HIPAA, so while not a 1 for 1 match, this could be used as a steppingstone to map an organization’s existing controls over to some of the data privacy laws.
SOC 2+ HIPAA
There is no direct mapping of SOC 2 TSCs to HIPAA Security or Privacy Rules that is publicly available, so a mapping of existing controls and newly generated controls will need to be developed. The rules cover all 5 TSCs.
The HIPAA Security Rule is strictly focused on the handling and management of personal health information (PHI) and is relevant to any organization that handles, interacts with, or manages PHI. As such, if your organization’s current scope does not address all systems that handle and manage PHI, the scope of the assessment would need to be expanded to include those systems and processes.
There is a mapping of the SOC TSCs to NIST CSF 1.1 which can then be aligned with the HIPAA Security Rule to better assist in the control identification.
SOC 2+ GDPR
There is a mapping of SOC 2 criteria to GDPR, however, most articles do not map, and additional control development will be needed. Of the controls that do map over, they map over to the Security and Privacy TSCs
Per the GDPR material scope, “This Regulation applies to the processing of personal data wholly or partly by automated means and to the processing other than by automated means of personal data which form part of a filing system or are intended to form part of a filing system.”
This would apply to any personal data of an individual within the European Union, regardless of where the data processor is located. The scope of GDPR is noted in Articles 2 & 3.
Enhancing Trust with SOC 2+ Reports
SOC 2+ reports offer a versatile and strategic solution for organizations needing to meet specific regulatory requirements alongside the standard SOC 2 framework. By incorporating additional compliance frameworks into the SOC 2 reporting process, companies can demonstrate their commitment to security and regulatory adherence in a comprehensive manner.
Whether through detailed mapping of existing controls to new frameworks or opting for a more rigorous SOC 2+ Examination, organizations can tailor their compliance reporting to meet the exact needs of their clients and regulators. For those considering the integration of SOC 2 with other regulatory frameworks, the benefits of operational transparency and client confidence make it a worthwhile endeavor.
If you are interested in adding other criteria/frameworks to your existing SOC Report or are new to SOC, LBMC can help. Reach out to our team to get started.







