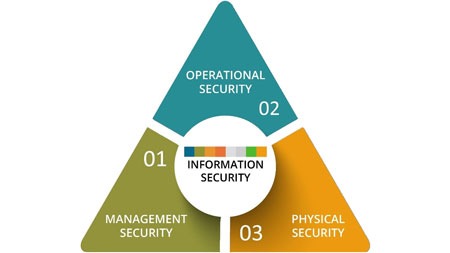
Did you know there are three categories of security controls?
Understanding these can help you build a robust security system tailored to your business needs.
- Management Security is all about your business policies, procedures, and governance—this includes different types of cyber security control measures.
- Operational Security checks if the safety measures you use in your business are working well.
- Physical Security protects your business assets from physical threats—after all, physical security is concerned with keeping your environment safe from unauthorized access and other risks.
Not Sure If Your Security Controls Are Enough?
Many organizations have security controls in place—but gaps often exist between policy, implementation, and monitoring.
The Foundation of Security
Comprehensive security is the key to any organization. There are three categories of security controls that businesses must consider: management security, operational security, and physical security. Each type is important for overall security and to protect against threats.
What is Management Security?
Management security is the overall design and governance of your security controls, often referred to as managerial security controls. These controls are crucial for setting the foundation of your digital security system and maintaining a secure environment.
Policies and Procedures
Define the rules for your security system. Your policies will cover areas such as security risk control, access control, incident response, and risk management. These guidelines give your employees a clear framework to follow, ensuring consistent security practices across the organization.
Risk Assessment and Security Management
Risk assessments look at your business risks, determines the impact of those risks and implements fixes which is a key part of security risk control. This proactive approach helps you allocate resources efficiently and strengthen your overall security management.
Security Awareness and Employee Training
Your employees need to understand the business policies for your security program and how they can help keep a secure environment. Security awareness and training programs will help them learn best practices and what steps they need to take to stay security aware. In this sense, your company can lower human mistake and improve general security.
Compliance and Auditing
Effective security programs need for your company to routinely assess its policies and regulatory requirements. Auditing and compliance help your company to satisfy industry requirements and follow security policies. Maintaining current security rules and spotting areas that require improvement depend on constant monitoring.
Example
An organization mandates that passwords change every ninety days as part of their security system. This policy is a top security protection measure that lowers the risk of unauthorized access. Frequent password changes make it harder for attackers to exploit compromised credentials, so it strengthens their overall security.
Would Your Security Governance Hold Up Under Audit?
Policies alone aren’t enough. Without clear ownership and enforcement, even well-designed controls can fall short.
How LBMC Helps Strengthen Security Controls
What is Operational Security?
Operational Security is the effectiveness of your controls. Also known as technical controls, these include types of security system components like access controls, authentication, internet security, and security topologies applied to networks, systems, and applications. Operational security is key to ensuring the technical controls you have in place are effective at protecting against threats.
Access Controls
Using access controls will limit who can use your system, applications and data within the business. These controls make sure only approved people see your sensitive information.
Authentication Mechanisms
Two forms of authentication that might assist your business add even more protection are passwords and multi-factor authentication (MFA). MFA lowers risk and ensures only authorized individuals may access your protected systems and data by combining multiple forms of identity.
Network Security
Network security uses firewalls, intrusion detection and prevention systems (IDS/IPS) to block cyber attacks and unauthorized access. By having strong network security, organizations can find and stop intrusions and keep their data safe and private.
Encryption
When data is being sent outside your business or just being stored, you need encryption to keep it safe. Encryption will change the data into a secret format so if someone gets access they can’t read it. Using strong encryption helps you protect data from theft and misuse.
Example
A Role-Based Access Control (RBAC) is a key allowing access to different parts of a system depending on a person’s position in your company. This reduces access and streamlines user rights, therefore facilitating management of who can view what and so enhancing security.
Are Your Security Processes Consistently Followed?
Strong controls depend on execution. Gaps in day-to-day processes can create risk—even when the right tools are in place.
What is Physical Security?
Physical security is the collection of actions taken to safeguard company assets—including personnel, data, hardware, and hardware from physical hazards that could compromise, damage, or disrupt your company. It covers security aspects including environmental control, access control, surveillance, and contingency preparation. Maintaining confidentiality, integrity and availability of systems, as well as business continuity in the face of unanticipated occurrences, depends on physical security.
Access Control Systems
Access control systems are critical to limit access to buildings or specific areas within an organization. These systems make sure only the right people can enter secure places. They help protect physical assets and people from dangers. Good access control systems keep these important areas secure.
Surveillance Systems
Surveillance systems, such as closed-circuit television (CCTV), are critical to monitor and record activities within an organization. These systems watch and records unauthorized activities and strange behavior giving valuable evidence that can show what happened if something goes wrong.
Environmental Controls
Environmental controls are key to maintaining the optimal conditions for sensitive equipment and data. These controls regulate temperature, humidity, and fire suppression systems to protect physical assets from environmental hazards.
Contingency Planning
Developing a disaster recovery and business continuity plan to make sure your business can continue in cases of disruption is what contingency planning is all about. These plans should outline the steps you need to take to recover from natural disasters, equipment failures or cyber attack incidents. When you are ready for emergencies, your business will have less downtime and keep important services running.
Example
Implementing biometric access controls like fingerprints or facial recognition is a practical security measure that offers high security by limiting access to authorized personnel only. These systems use unique biological characteristics such as fingerprints or facial recognition to prevent unauthorized access to a data center. Using biometric access controls can provide you with high security because only authorized people will be able to access sensitive areas and this protects your important information and systems.
Combining Security Controls for Maximum Protection
The three types of security controls are management, operational, and physical. They work together to form a strong security program. Combining these controls is a good way to defend against threats. Doing regular reviews and updating your systems are key to keeping your protection up-to-date. If you have questions or would like some more details, just ask!
Interconnecting Security Controls
Knowing how these security measures work helps your business maintain an effective security program. Deciding on a strategic mix of administrative, technical, and physical controls will depend on your risk and how your business needs to manage them.
Example
Where Security Controls Often Fall Short
Many organizations have security controls in place—but gaps tend to appear in how those controls work together.
- Policies are documented but not consistently enforced
- Tools are implemented but not regularly monitored or updated
- Responsibilities are unclear across teams
- Controls aren’t aligned to a recognized framework
- Documentation doesn’t hold up during audits
In most cases, the issue isn’t a lack of controls—it’s a lack of alignment between management, operational, and physical security.
When Should You Reevaluate Your Security Controls?
Security controls shouldn’t be static. It may be time for a closer look if:
- You’re preparing for an audit or compliance review
- Your organization is growing or adding new systems
- You’ve experienced a security incident—or a near miss
- You’re adopting cloud platforms or new technologies
- You’re unsure how your controls align with current frameworks
Even small gaps can create larger risks over time if they go unaddressed.
Building a Stronger Security Foundation
Effective security isn’t about having more controls—it’s about having the right controls working together.
A layered approach across management, operational, and physical security helps reduce risk, improve visibility, and support long-term resilience.
LBMC Cybersecurity helps organizations identify control gaps, align with industry frameworks, and strengthen their overall security posture through practical, real-world assessments.
Identify Gaps Before They Become Problems
Security controls should work together across your organization. A quick assessment can reveal where misalignment may be creating risk.