Home » Services & Solutions » Cybersecurity » Penetration Testing Services
LBMC Penetration Testing Services
Cyber-attackers are always on the lookout for vulnerabilities in your organization’s defenses. Take proactive steps to protect your data with LBMC’s Cybersecurity team. Our experienced experts perform thorough penetration testing on your networks, systems, and applications, adhering to industry standards, along with compliance standards like PCI DSS and other compliance frameworks.
We identify weaknesses, validate potential attack vectors, exploit vulnerabilities, and determine your environment’s susceptibility to attack without affecting your production systems. As one of the largest cybersecurity practices in Tennessee and a top penetration testing company LBMC helps safeguard your sensitive data.
Questions About Cybersecurity Services?
If you’re evaluating risks, preparing for an assessment, or responding to new security requirements, our team can help you understand your options and determine next steps.
Cybersecurity Insights — Delivered to Your Inbox
Stay informed on emerging threats, evolving compliance requirements, and practical strategies to strengthen your organization’s security posture.
What you’ll receive:
- Cybersecurity trends, threats, and risk insights
- Compliance updates across frameworks like HITRUST, CMMC, SOC, and NIST
- Practical guidance from LBMC cybersecurity advisors
- Invitations to webinars, events, and new resources
Enhance Your Security Posture with Advance Guard
Investing in cybersecurity resources and performing periodic penetration tests is not enough to protect your organization from evolving threats. You need continuous assessment and expert guidance to stay ahead of the game. That’s where Advance Guard comes in.
Advance Guard and Advance Guard+ offer a true “trusted security advisor” capacity. Our technical security experts work with your team to provide:
- Continuous Threat Assessments
- Monthly Red Team Activities
- Annual Security Training and Tabletops
- Security Team Extension
- Custom testing as needed.
With Advance Guard, you gain a partner that extends your security team, helping you to stay ahead of potential attacks. Advance Guard clients enjoy a 10% discount on technical projects, including penetration testing, web and mobile application testing, and incident response services.
Strengthen your security posture and protect your organization from potential threats with Advance Guard. View our sample annual engagement schedule with defined monthly tasks to see how we can help you stay secure.
Enhance Your Security Posture with LBMC Guard
Committing to quarterly vulnerability assessments and external attack surface management (EASM) is foundational for your cybersecurity posture, whether for baseline cyber hygiene or compliance requirements.

Our LBMC Guard offering is a proactive cybersecurity service that identifies and monitors an organization’s digital assets. The primary goals of EASM, combined with quarterly vulnerability assessments, are to reduce the risk of cyber-attacks by proactively discovering vulnerabilities and mitigating risks. By continuously monitoring your assets for threats, you can significantly improve your overall security posture.
LBMC Guard will provide this desired baseline. Our technical security experts work with your team to provide the following:
- External Attack Surface Management (EASM)
- Quarterly External Vulnerability Assessments
- Quarterly Internal Vulnerability Assessments
- Quarterly Web Application Vulnerability Assessments
External Attack Surface Management goes beyond traditional vulnerability scanning:
- Asset Discovery: We map out all your internet-facing assets, including unknown or forgotten ones, providing a complete picture of your exposure.
- Risk Management: By understanding your external attack surface, we can prioritize risks based on their potential impact, ensuring that critical issues are tackled first.
- Regulatory Compliance: Regular EASM helps in meeting compliance standards like GDPR, HIPAA, or PCI-DSS, which require ongoing vulnerability management and security assessments.
Quarterly vulnerability assessments are a key line of defense in identifying potential weaknesses before they can be exploited by cybercriminals. By performing external, internal, and web application assessments, you benefit from the following:
- Internal Assessments delve deep into your network, uncovering vulnerabilities that might be hidden from external views but could be exploited by insiders or through sophisticated attacks.
- External Assessments focus on your public-facing assets, ensuring that the first impression attackers get of your organization isn’t one of vulnerability.
- Web Application Assessments ensure that application vulnerabilities are identified and addressed before they can be exploited by malicious actors, significantly reducing the risk of security breaches.
With LBMC Guard, you gain a partner that extends your security team, helping you to stay ahead of potential attacks. LBMC Guard clients also enjoy a 10% discount on technical projects, including penetration testing, web and mobile application testing, and incident response services.
Strengthen your security posture and protect your organization from potential threats with LBMC Guard.
External Penetration Testing Services
LBMC’s external penetration testing services help you to assess the security posture of your internet-facing systems. By adopting the perspective of a hacker, we identify vulnerabilities and provide actionable recommendations to improve your existing security measures.
Our expert team uses advanced tools and techniques to conduct a thorough assessment, simulating real-world attack scenarios. We perform the assessment with little prior knowledge of your environment to identify weaknesses in your security defenses.
Our external penetration testing services can help you to:
- Identify and address potential security threats before they are exploited.
- Exceed regulatory compliance requirements for your industry.
- Enhance your overall security posture and protect your brand reputation.
Trust our expert team to provide you with the insights you need to protect your business.
Internal Network Penetration Testing Services
Ensure that your organization’s internal network is secure with LBMC Cybersecurity ‘s internal network penetration testing services. Using a trusted testing methodology, we identify weaknesses that unauthorized users could exploit.
Our process involves connecting to an active network port within the internal network or remotely. This approach simulates an attacker’s perspective, providing a comprehensive picture of security risks in your private IT environment.
Many organizations secure their perimeter but overlook internal network vulnerabilities. LBMC Cybersecurity helps identify and address these risks, offering recommendations to strengthen your network security.
Wireless Network Security Testing
Wireless networks are essential for business flexibility but bring security risks. LBMC can evaluate your wireless network security to protect against potential threats.
Our services include penetration tests and architecture design reviews to identify vulnerabilities hackers could exploit. We also assess your network segmentation design to make sure that it’s as secure as possible.
Our goal is to keep your sensitive information safe and prevent unauthorized access to your private network environment. Ensure your wireless network security with LBMC.
Social Engineering
We use various techniques to test your company’s vulnerability, such as sending fake emails, posing as callers seeking sensitive information, and conducting pre-texting phone calls. This process helps expose practices that create vulnerabilities and helps determine the vigilance and awareness of your personnel. Our service offerings are:
- Email Phishing — Crafting a tailored email message(s) that includes a link to a spoofed website. We will then send it to a focused audience that is agreed upon by the organization.
- Phone Testing (Pre-Texting) — Posing as a “trusted source” and asking for credentials or call the help desk and attempt to get a password reset.
- USB Drops — Dropping USB sticks around public areas of facilities to get users to insert them into their computer enabling a back door into the network or installing malware.
- Physical Testing — Evaluating your company’s physical security controls in place to protect your network and IT assets. From piggybacking into an office to cloning ID badges, we offer a wide range of options.
Web-Application Testing
Are you concerned about the security of your web application? LBMC Cybersecurity offers expert Web-Application Testing services to protect your application from potential attackers. Our experienced professionals use cutting-edge tools and techniques to identify and address any weaknesses.
Our testing methodology includes dynamic application security testing, simulating attacks by an attacker with limited prior knowledge. We employ manual and automated testing, intelligent fuzzing, access controls, application logic, authentication, and session management testing, adhering to the OWASP testing methodology with both commercial and open-source web application tools.
We conduct attack simulations from two perspectives: an unauthenticated attacker (has no access to the application) and basic or limited end-users with authenticated access. This approach provides you with a clear picture of any security weaknesses and the likelihood of a successful exploit.
Ensure the security of your web application with LBMC’s Web-Application Testing services. We provide thorough testing and analysis to protect your business from potential threats.
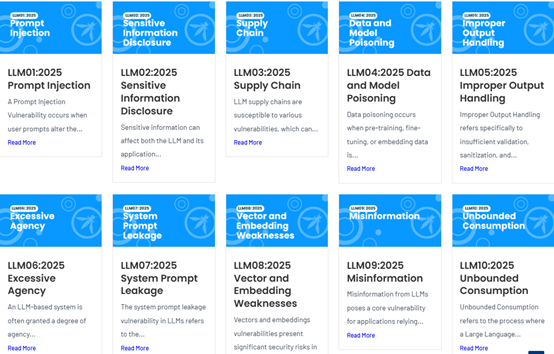
AI Application Security Testing Methodology
This assessment evaluates the security of your AI application(s) by examining the controls and trust boundaries of its supporting components. The engagement will target AI-specific threats and testing will follow a threat-driven methodology aligned with the relevant portions of the OWASP Top 10 for LLM Applications. The approach simulates realistic adversarial behavior to identify weaknesses that could be exploited in real-world attack scenarios.
Mobile Application Security Assessment
The aim of our mobile application security assessment service is to identify potential vulnerabilities that can be exploited by attackers and enhance the overall security posture of your in-scope iOS and Android applications.
LBMC’s Cybersecurity team will assess your application’s security by simulating public access from our mobile devices. We use both manual and automated testing methods, including intelligent fuzzing, access controls, application logic, authentication, and session management. While adhering to the OWASP Mobile testing methodology, our testing team combines commercial and open-source web application tools with their extensive experience in identifying and exploiting application security weaknesses across various industries. Our assessment will provide recommendations for improving your mobile application’s overall security.
Purple Teaming
Purple-teaming is a collaborative effort between a red team (penetration testing) and a blue team (network defense) to ensure effective security controls. Often, red and blue teams operate in silos, missing the opportunity for real-time testing and attack scenario simulation.
LBMC Cybersecurity bridges this gap by leveraging our extensive experience in both penetration testing and incident response. We work with your organization to select and test appropriate controls, including external perimeters, cloud environments, and internal controls. Our purple-teaming approach ensures your security controls are effective, and your organization is prepared to defend against cyber-attacks.
Cloud Security Assessment
Is your business protected against cloud-based security threats? With the increasing migration to cloud-based systems, ensuring the security of your cloud environment is essential. Traditional security assessment firms using automated tools often fall short in modern IT infrastructures, requiring a methodology grounded in experience and technical expertise.
LBMC Cybersecurity offers specialized cloud penetration testing services for IaaS, PaaS, and SaaS environments. Our expert team identifies and addresses security issues, providing comprehensive reports outlining potential vulnerabilities and remediation steps.
Trust LBMC to ensure your cloud environment is secure. We deliver high-quality, personalized cloud security assessments tailored to each of our clients. Choose LBMC Cybersecurity for peace of mind against cloud-based security threats.
Whether you’re assessing risk, preparing for compliance, or strengthening your security program, LBMC can help you move forward with clarity and confidence. Start with a conversation focused on what matters most to your organization.
Industries We Serve
Our cybersecurity advisory team works with organizations across industries to address security risks, compliance requirements, and operational challenges. We help clients strengthen controls, reduce exposure, and align security efforts with business priorities. Whether you’re responding to new regulations, supporting growth, or improving security maturity, our team provides clear guidance grounded in real-world experience.
All Industries We Support
Local Expertise, Wherever You Are
With offices in Chattanooga, Memphis, Louisville, Nashville, Knoxville, Philadelphia, and Charlotte, plus remote offices, LBMC partners with businesses across the region and beyond.
Executive Team
Let’s Talk About Your Cybersecurity Priorities
Whether you’re preparing for a compliance assessment, addressing security gaps, or strengthening your overall risk posture, LBMC’s cybersecurity advisors are ready to help. We’ll start with a conversation focused on your current environment, requirements, and the steps needed to move forward with confidence.