Home » Services & Solutions » Cybersecurity » Incident Response
Cyber Incident Response
One look at the constant news cycle illustrates just how vulnerable companies are to the whims of cyber-attacks. Therefore, the ability of today’s organizations to quickly and efficiently respond to a computer security incident has never been more critical. A proper response to network and computer attacks can prevent unneeded expense, over-extending internal resources, and provide the essential information needed to make critical decisions on how to move forward.
Questions About Cybersecurity Services?
If you’re evaluating risks, preparing for an assessment, or responding to new security requirements, our team can help you understand your options and determine next steps.
Incident Response
Our incident response methodology leverages the NIST-800-61 Computer Security Incident Handling Guide to determine answers to critical questions, such as:
When did the incident occur?
It is not uncommon to find that the intruders have been on networks for months before detected. Therefore, proper analysis is imperative to find out when the incident initially occurred so you can determine the timeframe of exposure.
Where did the incident occur?
Determining the point of initial compromise, and all locations of the compromise, is paramount to properly contain and eradicate the threat.
What was at risk?
Data breaches are arguably one of the most feared events for an organization to endure. This is an area where a thorough forensic analysis is beneficial. Just because a system has been compromised does not always mean that sensitive data was obtained. Understanding the extent of the compromise is vital to determine next steps.
How did the incident occur?
Understanding the root cause of the incident will provide the needed details for proper remediation. Our incident response reports provide immediate and long-term remediation steps to build resiliency against similar attacks moving forward.
Our goal is to leverage our extensive security and digital forensics expertise to assist our clients through computer security incidents while working to reduce the overall impact as much as possible. Being able to answer these questions during a computer security incident is paramount in numerous situations.
Incident Response Plans
An incident response plan is a documented plan/procedure for how the incident will be handled. While the contents may vary from organization to organization, most consist of standard operating procedures, processes, and communication plans. [Link to blog titled “Incident Response Frequently Asked Questions”]
Incident Response Programs and Training
We also work with organizations to elevate their incident response plans into proactive incident response programs. To assist our clients with this transition, LBMC Cybersecurity designs and delivers custom incident response tabletop exercises. Experience has demonstrated that this small investment in continuous improvement will pay dividends with faster response times, better communications, and lower costs when an incident does occur.
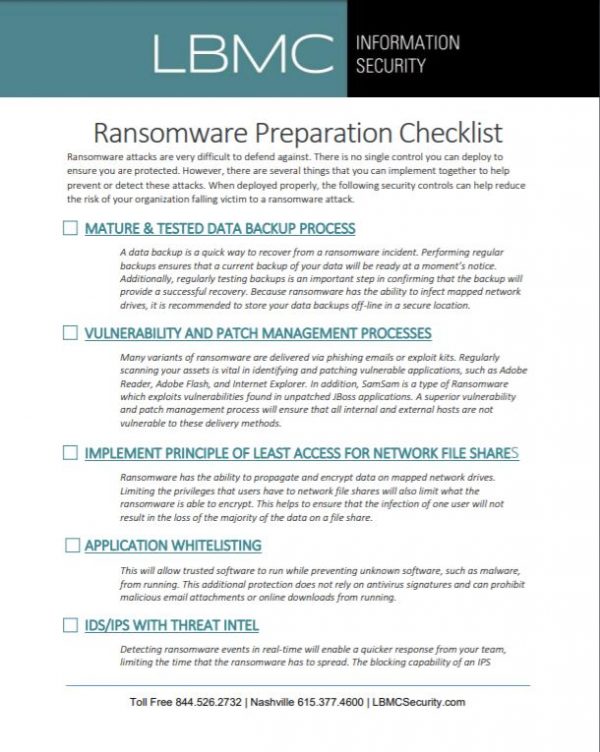
Ransomware Checklist
Includes detailed steps your organization can take to defend against ransomware.
Malware Compromise Assessment
Our Malware Compromise Assessment was designed on the premise that most organizations have a passive approach to malware protection. Billions of dollars are spent annually on products designed to detect an attacker, yet massive data breaches happen on a near-weekly basis.
Recent studies have determined that the time between compromise and detection, known as the “compromise detection gap,” averages five to eight months. In more than two-thirds of cases, the compromised organization is first notified of the breach by a third party, such as law enforcement.
We use a “converged security” approach that gathers and analyzes both network information and endpoint information and correlates the captured data with threat intelligence.
Dissolvable Agents Save Time and Money
In the past, thorough threat hunting services required full endpoint agents to be installed and later uninstalled on each computer. Our malware compromise assessment does not require the installation of a full client agent. It gathers this information using an innovative “dissolvable” agent on Windows and Linux endpoints. This shortens the project timeline to a few weeks as opposed to many months.
Threat Intelligence and Malware Analysis
LBMC Cybersecurity’s threat intelligence uses a large catalog of data, including open-source threat intelligence from multiple sources, up-to-the-minute data from CyberMaxx, and multiple commercial threat feeds. For artifacts that cannot be identified as either benign or malicious through threat intelligence, we perform network traffic heuristics and manual malware analysis.
Tabletop Exercises
The most crucial step in developing an incident response plan is to stress test the plan before a real incident occurs. Ask yourself:
- Does your plan include everything needed to successfully address an incident?
- Are the contacts and communication plans accurate to your organization?
- Does it need revisions or updates?
- Does it add any value outside of a checkbox for compliance?
- How do you know if it actually provides the intended value?
We can help design and facilitate an incident response tabletop session to help you improve your incident response program. Our team will provide consulting services to help you design, plan, and execute table top exercises to practice your incident response (IR) plan, help personnel understand their obligations and duties in the event of a security incident, and evaluate the IR plan’s robustness concerning communication, responsibilities, and governance. The test will also include documentation of results and an after-test review to evaluate the test process, specific responses, successes, failures, and lessons learned.
Instead of making assumptions and simply placing your incident response documentation on a shelf and hoping it is accurate, it’s better to test it with tabletop exercises designed to build continuous improvement into your incident response program before your next incident occurs. Designed correctly, tabletop exercises can help you determine how well your people, processes, and technologies are prepared for an incident. More importantly, these exercises allow you to improve that preparation over time.
If you’re navigating complex security, compliance, or risk challenges, LBMC’s cybersecurity advisors can help you prioritize next steps with clarity. Start with a conversation focused on your goals, risks, and operational realities.
Industries We Serve
Our cybersecurity advisory team works with organizations across industries to address security risks, compliance requirements, and operational challenges. We help clients strengthen controls, reduce exposure, and align security efforts with business priorities. Whether you’re responding to new regulations, supporting growth, or improving security maturity, our team provides clear guidance grounded in real-world experience.
All Industries We Support
Local Expertise, Wherever You Are
With offices in Chattanooga, Memphis, Louisville, Nashville, Knoxville, Philadelphia, and Charlotte, plus remote offices, LBMC partners with businesses across the region and beyond.
Executive Team
Let’s Talk About Your Cybersecurity Priorities
Whether you’re preparing for a compliance assessment, addressing security gaps, or strengthening your overall risk posture, LBMC’s cybersecurity advisors are ready to help. We’ll start with a conversation focused on your current environment, requirements, and the steps needed to move forward with confidence.

