Home » Services & Solutions » Cybersecurity » Technical Security Services
Technical Security Services
The most effective way to defend your organization is to think like an attacker. LBMC’s technical security services help organizations identify exploitable weaknesses, simulate real-world attacks, and prepare for cyber incidents through penetration testing, incident response, and ransomware readiness assessments.
Our team combines offensive security techniques with practical remediation guidance to help you reduce risk, strengthen defenses, and respond confidently to evolving threats.
Questions About Cybersecurity Services?
If you’re evaluating risks, preparing for an assessment, or responding to new security requirements, our team can help you understand your options and determine next steps.
What Are Technical Security Services?
Technical security services focus on identifying, validating, and reducing cybersecurity risk through hands-on testing and real-world attack simulation.
These services go beyond policy and compliance. They actively test your environment to uncover how attackers could gain access, move through systems, and impact operations.
At LBMC, this includes:
- Penetration testing and adversary simulation
- Incident response readiness and support
- Ransomware resilience assessments
- Vulnerability and exposure analysis across systems and infrastructure
When Organizations Use Technical Security Services
Organizations typically invest in technical security services when they need to validate their defenses or respond to increasing risk.
Common triggers include:
- Preparing for a penetration test required by clients or regulators
- Responding to a recent security incident or ransomware concern
- Evaluating internet-facing systems and vulnerabilities
- Supporting cyber insurance or audit requirements
- Validating security controls after cloud migration or system changes
- Addressing board or leadership concerns around cyber risk
Cybersecurity Insights — Delivered to Your Inbox
Stay informed on emerging threats, evolving compliance requirements, and practical strategies to strengthen your organization’s security posture.
What you’ll receive:
- Cybersecurity trends, threats, and risk insights
- Compliance updates across frameworks like HITRUST, CMMC, SOC, and NIST
- Practical guidance from LBMC cybersecurity advisors
- Invitations to webinars, events, and new resources
Who Needs Technical Security Services?
Technical security services are designed for organizations that need to validate their defenses and understand real-world risk exposure.
These services are especially valuable for:
- Organizations with internet-facing systems or sensitive data
- Companies preparing for audits, cyber insurance, or client security requirements
- Teams responding to ransomware threats or recent security incidents
- Businesses undergoing cloud migration, system changes, or rapid growth
- Leadership teams seeking visibility into actual security risk—not just policy compliance
Our Technical Security Services
LBMC’s technical security services help organizations identify vulnerabilities, simulate real-world attacks, and prepare for cyber incidents. Whether you’re proactively testing your defenses or responding to emerging threats, our team provides the insight and support needed to strengthen your security posture.

Core Technical Security Services
Advanced Technical Security Assessments
Flash Security Assessment
A rapid, high-impact assessment designed to identify critical vulnerabilities and prioritize remediation efforts quickly.
External Vulnerability Assessment
We evaluate your internet-facing systems to identify exposed services, vulnerabilities, and weaknesses that could be exploited by attackers.
Open-Source Intelligence (OSINT) Analysis
We assess publicly available information—including breach data, repositories, and social platforms—to identify sensitive data exposure and potential attack vectors.
Active Directory Security Assessment
We evaluate your Active Directory environment to identify risks related to credentials, privileged access, lateral movement, and attack paths—one of the most common entry points for attackers.
Solutions Built Around Your Goals
Whether you’re managing complexity, preparing for growth, or exploring new opportunities, LBMC delivers practical guidance and strategic support to help you move forward with confidence.
Ransomware Readiness Assessment
Ransomware continues to evolve into highly targeted, disruptive attacks that impact both on-premises and cloud environments. Many organizations invest in security controls but lack validation of whether those controls will perform under real-world attack conditions.
LBMC’s ransomware readiness assessment evaluates your organization’s ability to prevent, detect, and respond to ransomware using a structured, scenario-based approach.
Our methodology includes:
- Simulation of ransomware attack scenarios
- Evaluation of controls across people, processes, and technology
- Alignment with frameworks such as MITRE ATT&CK and D3FEND
- Actionable recommendations to improve resilience and recovery
This approach provides confidence that your organization is prepared for modern ransomware threats.
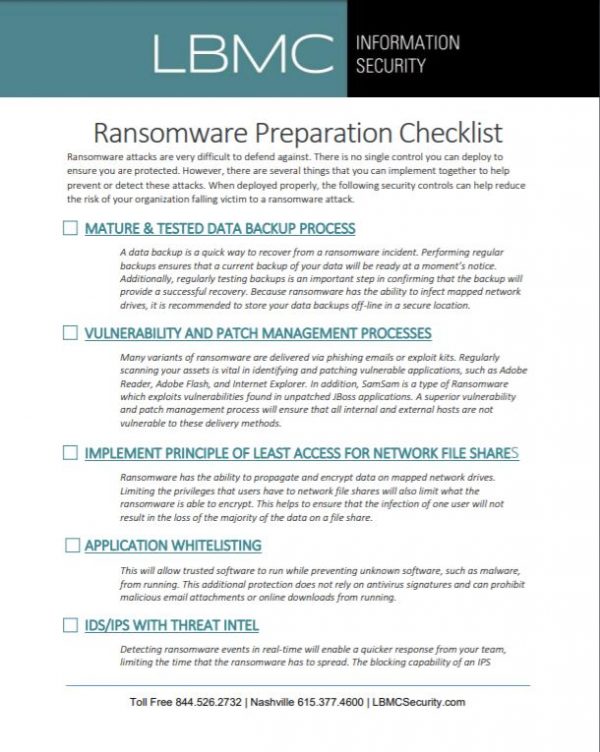
Ransomware Checklist
Includes detailed steps your organization can take to defend against ransomware.
What You Get from a Technical Security Engagement
LBMC delivers clear, actionable outputs to help you prioritize and remediate risk:
- Detailed findings report with severity rankings
- Identification of exploitable vulnerabilities and attack paths
- Prioritized remediation recommendations
- Executive summary for leadership and stakeholders
- Guidance for improving detection and response capabilities
- Optional retesting to validate remediation efforts
Why Choose LBMC for Technical Security Services
LBMC combines deep technical expertise with real-world experience to deliver meaningful, actionable results.
What sets LBMC apart:
- Experienced penetration testers and incident response professionals
- GIAC-certified expertise in incident handling and offensive security
- Practical, business-aligned recommendations—not just technical findings
- Proven approach across complex, regulated environments
- Integrated cybersecurity services spanning advisory, compliance, and technical testing
Industries We Support
Our cybersecurity advisory team works with organizations across industries to address security risks, compliance requirements, and operational challenges. We help clients strengthen controls, reduce exposure, and align security efforts with business priorities. Whether you’re responding to new regulations, supporting growth, or improving security maturity, our team provides clear guidance grounded in real-world experience.
All Industries We Support
FAQs About Technical Security Services
What is the difference between penetration testing and vulnerability assessments?
Vulnerability assessments identify weaknesses, while penetration testing actively attempts to exploit them to demonstrate real-world risk.
How often should penetration testing be performed?
Most organizations perform penetration testing annually or after significant infrastructure changes.
What is an incident response retainer?
It provides immediate access to security experts during an incident, helping reduce response time and limit damage.
What is a ransomware readiness assessment?
It evaluates your organization’s ability to prevent, detect, and recover from ransomware attacks.
Why is Active Directory security important?
Active Directory controls access across users and systems, making it a primary target for attackers seeking to escalate privileges and move laterally.
Local Expertise, Wherever You Are
With offices in Chattanooga, Memphis, Louisville, Nashville, Knoxville, Philadelphia, and Charlotte, plus remote offices, LBMC partners with businesses across the region and beyond.
Let’s Talk About Your Technical Security Needs
Whether you’re preparing for a penetration test, strengthening your incident response capabilities, or evaluating ransomware readiness, LBMC can help you identify risks and take the next step. We’ll start with a conversation focused on your environment, priorities, and security goals.