Employees can unknowingly fall prey to a phishing attack with just one click. That one tiny click can shake your business’ foundation to the core. After all, the average cost of a single data breach in the U.S. in from 2006 to 2024 was $9.36 million. It’s up to your company to educate your employees on how to identify malicious emails.
Cybersecurity Sense Podcast: Not All Phishing Assessments are Equal
In this episode, LBMC’s cybersecurity experts discuss the topic of social engineering via phishing. Learn the difference in using phishing software solutions versus penetration testing services for your cybersecurity program.
What is phishing?
Phishing is a type of cybersecurity attack during which a hacker sends an email with a link or document that looks legitimate but is designed to steal information. A phishing email looks as though it’s from a trusted source (e.g., your bank, another employee, a well-known company). Once someone clicks on the malicious link or attachment, however, he or she will be prompted to enter confidential information. The link could also download malware onto the employee’s device. Employees could hand hackers precisely what they need to gain access to important company accounts without ever knowing what happened.
Are there different types of phishing?
Phish can appear in different forms from generic to highly targeted. It’s important to understand the differences in order to properly respond to a phishing attack. Here are the main types of phishing attacks and a brief description of each attack’s goals.
- Phishing—Generic attempts via email to acquire sensitive information by tricking users.
- Vishing—Cold calls to an entity, attempting to trick the recipient of the phone call into performing some action.
- Spear phishing—Targeted phishing attempts aimed at specific individuals or groups within an organization, where the attempts are personalized to increase credibility.
- Whaling—Highly targeted attempts, using email as the communication medium to gather sensitive information from high-value individuals within an organization.
- Smishing—Phishing attempts via SMS or text messages to trick users into revealing sensitive information or performing certain actions.
- Qishing—Attackers replace legitimate QR codes with malicious ones, leading users to phishing sites or malware downloads.
How do cybercriminals craft convincing phishing attacks?
Phishing attacks are cybercrimes conducted through email, telephone, or text messages, typically performed by a cybercriminal posing as an institution or a trusted person to trick individuals into offering personal information, banking or credit card details, and other types of sensitive data. Cyber-criminals use this sensitive data to access bank accounts and steal identities. The following is a brief overview of the anatomy of a phishing attack and what IT can do to help prevent, detect, and respond to phishing campaigns.
Taking into consideration a high-level overview, it’s good to focus on how a threat actor may achieve the initial foothold on a corporation’s systems before pivoting mercilessly to harvest sensitive data. When considering this initial foothold, the following approach outlines some steps that can demonstrate how the process works.
- Research the Company— Initial research is done on the fake company to understand organizational structure, business drivers, vendors, employee’s social media content, and other information repositories.
- Obtain a List of Emails—When the company information is known, along with some good phishing approaches, it’s time to harvest publicly available emails, in addition to “mangling” (see below) known employee names.
- Decide Where the Email Should Originate—With the knowledge of the company, internal personnel, and a list of emails, the next step involves figuring out where the email should originate. This could involve purchasing a domain name similar to the fake company’s or another business the company is associated with.
- How to Mangle a Domain— Mangling a domain is a common technique for phishermen to use when they want their message to appear as if it’s from someone at a given company. Mangling a domain can be performed with multiple tools and consists of taking a list of known ways to mistype a domain, while still having it resemble the original domain.
- Strategize What You Want Phishing Targets to Do—A common approach is to clone a familiar website that resembles the fake company’s login portal users would authenticate to, or develop a document with malware that someone inside the company would likely open.
- Use AI-Generated Content to Supercharge Social Engineering—AI-driven tools can generate highly personalized phishing emails, realistic synthetic voices, or even deepfake videos to impersonate key personnel or trusted contacts. This tactic enhances credibility, making it easier to deceive employees into divulging sensitive information or clicking on malicious links, significantly increasing the success rate of the initial foothold attempt.
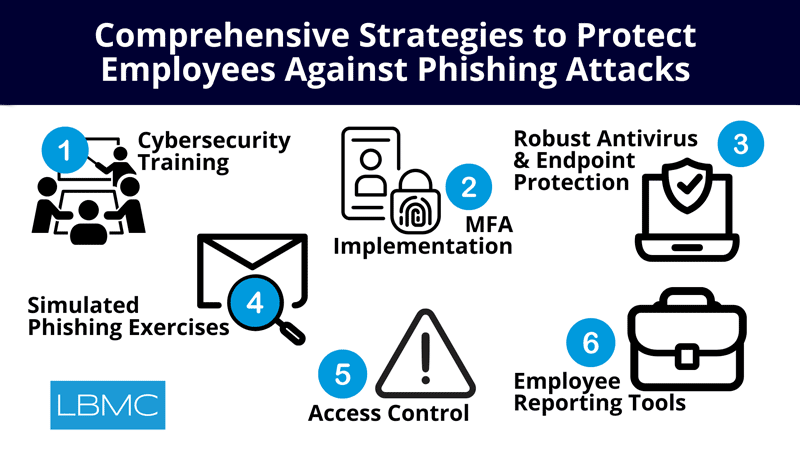
Comprehensive Strategies to Protect Against Phishing Attacks
1. Engaging Cybersecurity Training and Awareness
Provide engaging, mandatory cybersecurity training for all employees during onboarding and in regular refreshers. Focus on recognizing phishing indicators—like typos, generic greetings, suspicious email domains, and unsolicited attachments—using real-world examples of breaches to underscore risks. Include interactive elements, such as quizzes and simulations, to reinforce skills and encourage active participation.
2. Multi-Factor Authentication (MFA) Implementation
Enforce MFA across all systems to add an extra layer of security. This ensures that even if login credentials are compromised, unauthorized access is still prevented by requiring secondary verification.
3. Robust Antivirus and Endpoint Protection
Deploy and maintain up-to-date antivirus software across all devices, including personal ones used for work. IT should monitor and update protections frequently to reduce potential impacts of phishing-related breaches.
4. Simulated Phishing and Effectiveness Assessments
Regularly conduct simulated phishing exercises to assess employee responses, identify knowledge gaps, and measure training effectiveness. Tailor future training based on assessment results to continually improve awareness.
5. Email Filtering and Domain Spoofing Prevention
Implement a robust email gateway with spam and phishing filters, flagging external emails and suspicious domains. Consider using DomainKeys Identified Mail (DKIM) and tools like DNSTwist to proactively block “mangled” domains that closely mimic legitimate ones.
6. Access Control and Least Privilege
Limit access to sensitive data and systems only to employees who need it, reducing potential damage in case of a breach. Avoid granting broad administrative rights to minimize the risk of privilege misuse.
7. Restrict External Email Access Where Unnecessary
Regularly evaluate which employees genuinely require external email access, and remove these permissions for those who do not. Limiting exposure to external emails helps mitigate phishing risks by reducing the number of potential entry points for attackers.
8. Regular System Updates and Patch Management
Ensure all systems and applications are routinely updated with the latest patches to prevent exploitation of known vulnerabilities. Regular patch audits are crucial to sustaining a secure environment.
9. Backup and Recovery Readiness
Maintain verified, up-to-date backups of critical data and test them periodically to confirm successful restoration in the event of a ransomware attack or other data loss incident.
10. Employee Reporting Tools and Visual Cues
Equip employees with easy-to-use reporting tools (e.g., “Report Phishing” buttons in email clients) to flag suspected phishing emails quickly. Consider visual cues like employee photos in the email directory to help verify internal communications and reduce impersonation risks.